Some Known Details About It Service Melbourne
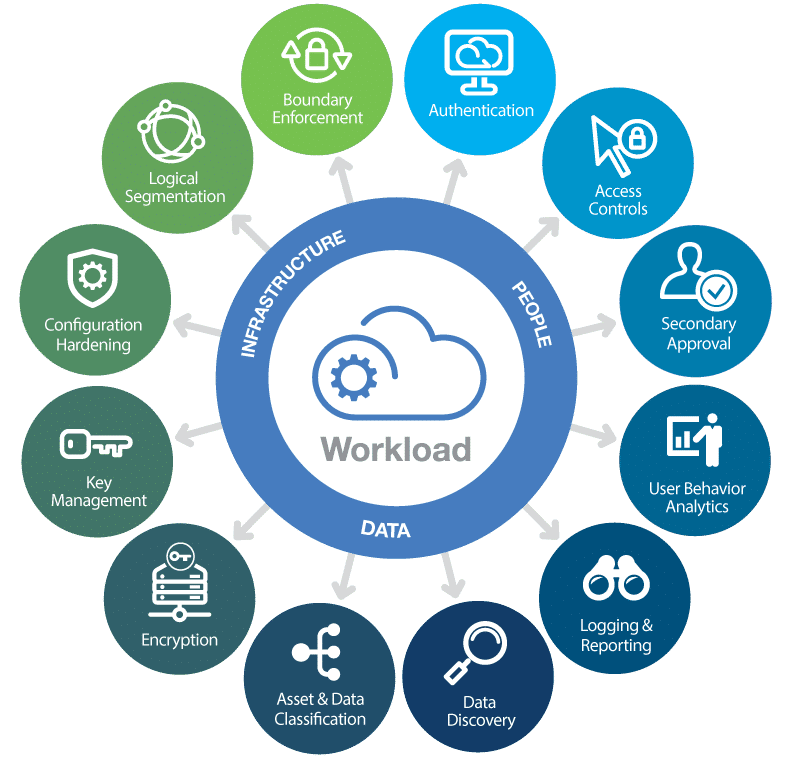
These policies have multi-factor authentication, protecting against out of the state logins and numerous various other ones in an excellent role. This is incredibly for the business that enable staff members to utilize their own phones for performing tasks. This bring-your-own-device (BYOD) is not every usual, but still exists. The support supplying companies place their group to protect that information as well as assets from cyberpunks or abuse.
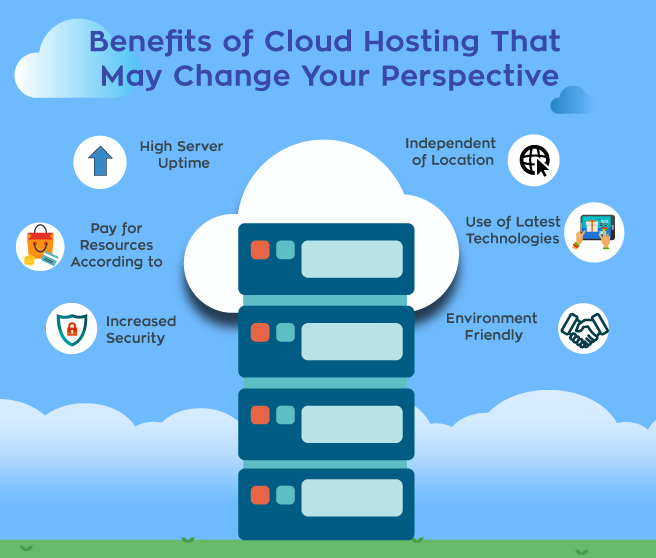
It ensures that only safe gadgets will certainly have the ability to execute from another location, as they would certainly be qualified of securing the delicate data of the business. It describes the on-demand schedule of computer system sources, including data storage space as well as computer power. This taking place does not require any type of straight active monitoring by the user.
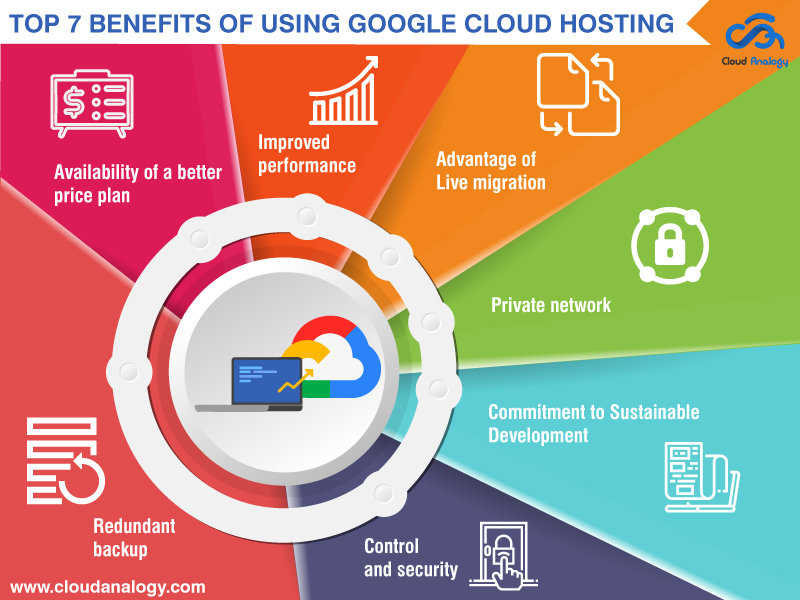
As its benefits are impressive, an increasing number of firms have actually begun changing to the cloud for organizing their data. managed it services melbourne. For keeping their secret information about consumers as well as their client experience (CX) safe, it comes with some phenomenal security attributes. The tech assistance group handles it well in 2 methods: Making sure configuring and taking care of the cloud system for holding a number of requisite applications, information administration, IT sustain and also downtime, Providing the full protection to what comes under the managed IT solutions from cyber lawbreakers.
9 Easy Facts About Managed It Services Melbourne Explained

Something failed. Wait a minute and attempt again Try again.

Companies are increasingly relocating their IT infrastructures right into the cloud. Many venture organizations now run in multi-cloud environments or make use of hybrid on-premises as well as cloud-based IT architectures.
7 Easy Facts About Managed It Services Melbourne Described
Information backup and recuperation support consist of the application of information backup options, such as cloud-based, disk-based and tape-based back-ups. Information back-up and recuperation assistance Includes screening information recuperation remedies to guarantee that they are reliable and also effective Read More Here in the event of an information loss or corruption. IT sustain is important for businesses that rely heavily on their information, such as those in the health care and financing sectors - it service melbourne.
Workplace innovation alters rapidly as well as gets much more complex by the year. Whereas the bulk of occupational computing when occurred within the office wall surfaces as well as inside a secure boundary, today's distributed workforce carries out service from Extra resources houses, cafe, cars and trucks literally anywhere with web gain access to. Sustaining and securing the myriad devices as well as access points employees now rely upon to stay effective has developed a whole lot more benefit IT groups that typically are already spread also slim.
Organizations resort to taken care of providers (MSPs) for a variety of factors, yet a lot of generally, they are utilized by organizations without any interior IT team or those that wish to use their internal IT professionals to concentrate on certain efforts as opposed to functional obligations for taking care of modern technology. MSPs supply a large range of services from the basics such as aid workdesk assistance as well as keeping IT tools and also services functioning all the means as much as giving the complete collection of IT capacities, including cyber security, internet connection, application assistance, data back-ups, and disaster recuperation.

The Facts About Managed It Services Uncovered
Managed IT solutions are much from one-size-fits-all, so partnering with an MSP that understands your company as well as is proactively spent in helping you fulfill your goals is vital.
Prospective threats outside the network are avoided, ensuring that a company's delicate data remains within. Organizations can go even more by specifying additional internal boundaries within their network, which can give better security as well as accessibility control. Gain access to control defines individuals or teams and the devices that have access to network applications and also systems thereby denying unsanctioned gain access to, as well as perhaps dangers.
A vulnerability is a bent instance in a software system and a make use of is an attack that leverages that vulnerability to gain control of that system. When a manipulate is introduced, there is often a window of opportunity for assailants to exploit that vulnerability before the security spot is applied.
Sandboxing is a cybersecurity practice where you run code or open documents in a risk-free, isolated setting on a host equipment that internet imitates end-user operating settings. Sandboxing observes the files or code as they are opened up and searches for malicious habits to stop risks from obtaining on the network. For example malware in data such as PDF, Microsoft Word, Excel and Power, Point can be safely found and blocked prior to the files get to an innocent end customer.